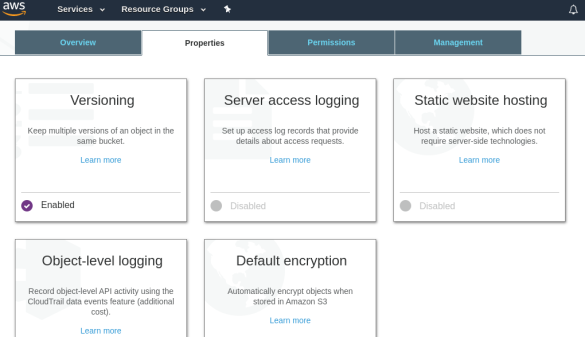
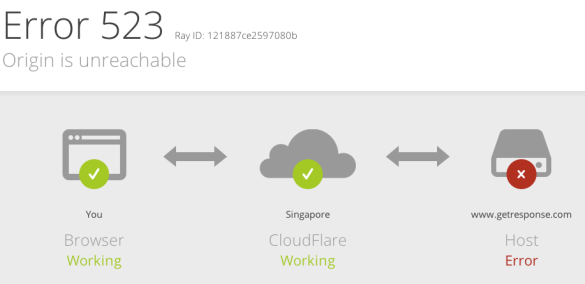
Saat tulisan ini dibuat, GetResponse.com sedang mengalami serangan DDoS. Response yang ditampilkan saat mengakses GetResponse.com adalah status code HTTP Error 523. Screen shot nya seperti di bawah ini:
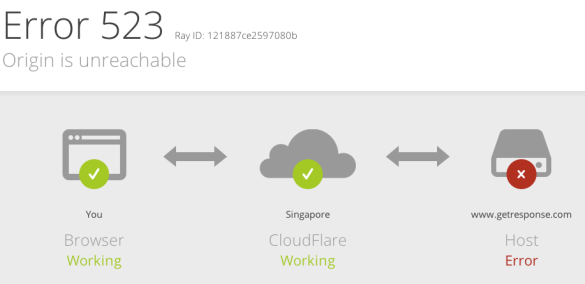
Http status code response error 523
Gambar tersebut terlihat bahwa sebelum request (permintaan) saya melalui browser ke http://www.getresponse.com dapat terjawab, ada satu entitas yang menjembatani, yaitu CloudFlare. CloudFlare adalah penyedia layanan content delivery network dan distribusi domain name server yang menyasar klien yang membutuhkan pengembangan kinerja dan kecepatan web server disertai keamanan. Gambar di atas juga memperlihatkan bawha browser klien dan CloudFlare bekerja normal, sedangkan website http://www.getresponse.com diinformasikan error.
HTTP response status code error 523 dikirimkan dari CloudFlare ke browser visitor saat CloudFlare tidak dapat mencapai server GetResponse.com. Gagalnya CloudFlare mencapai server getresponse.com salah satu sebabnya adalah miss setting domain name server di sisi website getresponse.com. Kode status error HTTP sebagai respon dapat dilihat lengkap di http://en.wikipedia.org/wiki/List_of_HTTP_status_codes.
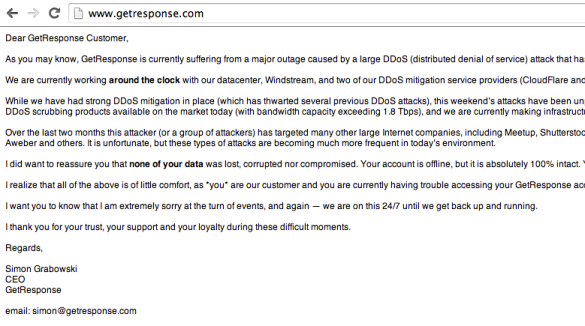
Penasaran apa yang sebenarnya terjadi, refresh sekali lagi website http://www.getresponse.com. OMG! Ternyata getresponse.com sedang mengalami serangan DDoS. Saat ini tampilannya bukan lagi error 523, tapi sudah pernyataan resmi CEO GetResponse, Simon Grabowski. Berikut di bawah ini adalah screen shot-nya.
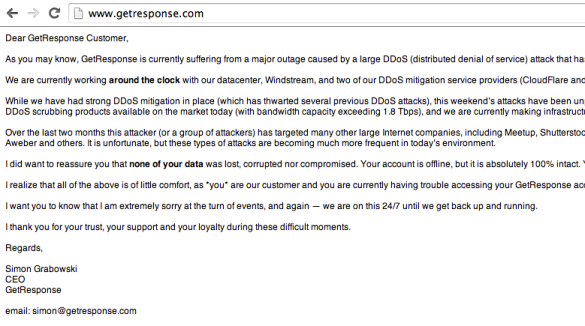
Pernyataan CEO Simon Grabowski tentang serangan DDoS yang dialami GetResponse
Serangan DDoS akhir-akhir ini banyak dialami oleh website MeetUp, ShutterStock, Aweber, MailChip, Survey Gizmo, HootSuite dan lainnya. Sekalipun GetResponse sudah menggunakan service mitigasi serangan website seperti dari CloudFlare dan Akamai/Prolexic namun tetap saja serangan DDoS membuat GetResponse down.
Berikut pernyataan resmi CEO GetResponse selengkapnya:
Dear GetResponse Customer,
As you may know, GetResponse is currently suffering from a major outage caused by a large DDoS (distributed denial of service) attack that has flooded our network and our datacenter with malicious traffic. As a result, our network is currently offline.
We are currently working around the clock with our datacenter, Windstream, and two of our DDoS mitigation service providers (CloudFlare and Akamai/Prolexic) to mitigate this attack and implement a permanent solution to fix this problem.
While we have had strong DDoS mitigation in place (which has thwarted several previous DDoS attacks), this weekend’s attacks have been unprecedented in scale and volume. We have decided to engage the most advanced and most powerful anti-DDoS scrubbing products available on the market today (with bandwidth capacity exceeding 1.8 Tbps), and we are currently making infrastructural changes to get it done.
Over the last two months this attacker (or a group of attackers) has targeted many other large Internet companies, including Meetup, Shutterstock, MailChimp, Fotolia, Basecamp, oDesk, SurveyGizmo, MadMimi, OkCupid, HootSite, Typepad, Elance, Aweber and others. It is unfortunate, but these types of attacks are becoming much more frequent in today’s environment.
I did want to reassure you that none of your data was lost, corrupted nor compromised. Your account is offline, but it is absolutely 100% intact. You will be able to access all of your data immediately after we come back up.
I realize that all of the above is of little comfort, as *you* are our customer and you are currently having trouble accessing your GetResponse account, unable to send your newsletters.
I want you to know that I am extremely sorry at the turn of events, and again — we are on this 24/7 until we get back up and running.
I thank you for your trust, your support and your loyalty during these difficult moments.
Regards,
Simon Grabowski
CEO
GetResponse
email: simon@getresponse.com